You
might have noticed a tremendous increase number of hack attacks on
wordpress, joomla blogs and other content managing systems. What the
hackers are doing is that instead of targeting the CMS itself meaning
wordpress or joomla. They are targeting a vulnerable website on a
server, Once they gain access to a single vulnerable website on the
server, They upload a shell and with a method called "Symlink Bypass". They
manage to extract the configuration files of another website hosted on
that same server and later on using a simple MySQL interface they
connect to that website.
What Is Symlink Bypass?
Well, I would not like to go into much detail. However for your
understanding all you need to know is that symlink is a method to
refrence other files and folders on linux. Just like a shortcut in
windows. Symlink is necessary in order to make linux work faster.
However symlink bypassing is a method which is used to access folders on
a server which the user isn't permitted. For example the home directory
can only be accessed by a root level user. However with symlink bypass
you can touch files inside home directory.
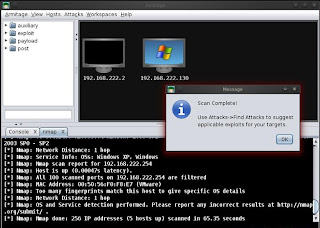
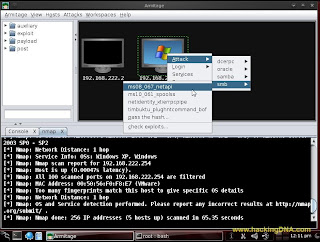
Step 1 - The hackers searches for a vunerable website on a
server. A hacker can get list of domains on a webserver by doing a
reverse iP lookup.
Step 2 - Next the hacker hacks into any vulnerable website on the server and upload a PHP shell.
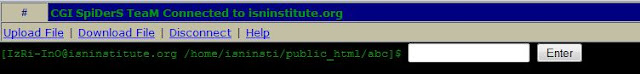
Step 3 - The above picture demonstrates two files one named
.htacess and the second named jaugar.izri being uploaded to the server.
Here is what Jaugar.izri looks like when it's made public by adding 0755
permissions.
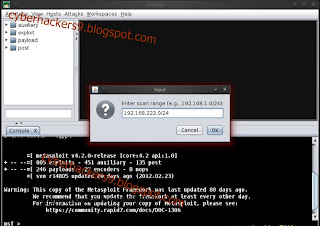
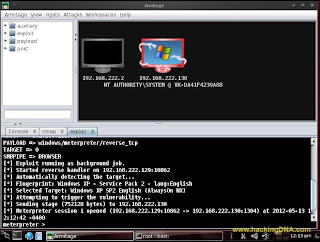
Step 4 - The hacker connects to the izri script and then gives the following commands
mkdir 1111
cd 1111
ln -s / root
ls -la /etc/valiases/(site.com)
The
first command creates a directory named 1111(Mkdir 1111). The next
command navigates to the directory(cd 1111). The third command creates
the symlink of the root. The fourth command will extract the user name
of the website you put in place of site.com.
The target website is entered in ls - la /etc/valiases/site.com.
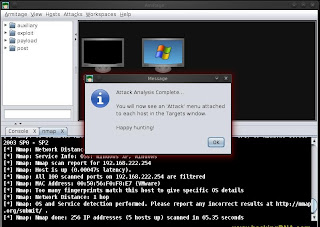
The
above screenshot explains the whole story. The hacker then navigates to
the "1111" directory and the configuration file of the target website
is created there. The hacker downloads the configuration files and uses
the information to access the database and there he can make any
changes.
How To Be Protected?
There is nothing much you can do it on your end, else then renaming your
config and moving it to a safer place. If you are worried about your
website's security, Feel free to contact me.